Security awareness training for employees helps small business owners mitigate risks against cybersecurity threats
Managed IT services and other technical controls, such as firewalls, antivirus software and security software, help protect your business data security, but by no means are they enough. Many businesses all but ignore the number one risk to their business security…. HUMANS. Yes, your employees are talented and knowledgeable in their respective roles. But, they are not IT or security experts, and you really can’t expect them to be.
It's important to understand how employees compromise your data security and then equip them with security training and resources. Otherwise, without proper training and awareness, your team is vulnerable to exposing your business to a real security risk.
How does my team compromise my business and its cybersecurity?
From accidents to ignorance to trickery, there are some common ways your employees put your business at risk.
They are deceived.
The vast majority of successful cyber attacks occur not because some hacker exploited a technical loophole, but because your own employee virtually opened the door. According to Verizon , 94% of all malware stems from email, with a whopping 80% of reported attacks coming from phishing email. More importantly to small businesses is the finding that organizations with 1-250 employees have the highest targeted malicious email attack rate. (Symantec)
With more of our data online and accessible to the outside public, social engineering and phishing scams become more sophisticated. Social engineering refers to the use of deceptive tactics to manipulate someone into providing personal information that may be used in cyber attacks. One of the most common ways the information is used is within phishing scams, fake email messages that seem to come from a reputable source but trick a person into providing sensitive information such as passwords or credit card numbers.
These scams are extremely sophisticated,and, without proper training, employees can be duped into clicking on a malicious link or providing confidential business information and leaking other sensitive data.
They introduce infected devices.
One of the advantages of a small business is its flexibility. Employees are often empowered with mobile devices and, in many cases, use personal mobile devices to access company data. However, these personal smartphones, tablets, or laptops can expose your business to a security breach. If an employee accesses your network with an operating system that is already infected with malware or other malicious code, it can potentially spread to your IT environment. Oftentimes, a person doesn’t even know their device is compromised until long after it’s infected. In fact, according to IBM, the average time to identify a breach is 206 days. That's almost 7 months!
As your millennial workforce grows, this risk will only increase. As a generation who literally grew up with technology, their comfort-level with their devices often results in a more laid-back approach to cybersecurity. Even with proper technical controls for mobile devices, users may try to circumvent that with their personal devices in order to work more efficiently.
Without setting expectations and increasing awareness, employee devices add a real risk to your security.
Oops! They make a mistake.
Your employees are human – they are going to make mistakes. It happens to the best of us at some point. Many of these mistakes do not really pose any threat to data security, such as dropping and damaging their company smartphone. However, some mistakes do result in security concerns. Common oversights include having a laptop stolen from their unlocked car, writing down and posting passwords, forgetting to lock their screens when they leave their workstation, or mistakenly sending a sensitive email to the wrong person.
Human error is ultimately inevitable; you can’t fully eradicate it. However, by increasing security awareness and educating your team on malware, phishing scams, and other types of cybercrime you can help to reduce its occurrence and some of your risk.
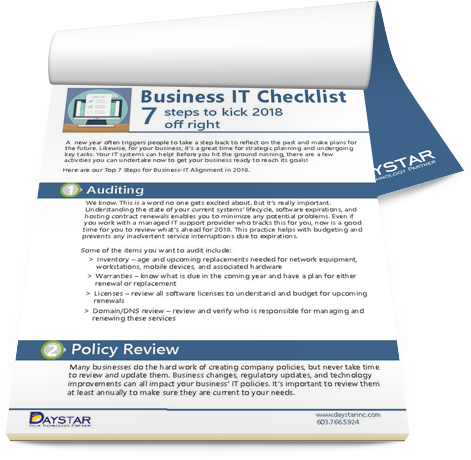
What do they need to know about cybersecurity?
One of the most basic ways to educate employees about security is to define, document, communicate, and enforce a written information security policy (WISP). All employees should be required to read and sign the company WISP.
Your WISP should define your security procedures and policies, including:
- Strong Passwords
- Email usage
- Access control (including multi-factor authentication)
- Approved software
- Acceptable use
- Blogging and social media usage
- Physical access (such as locking computer screens, etc.)
It’s important to make this more than just another HR document new hires must sign. All employees should read and sign the WISP annually. The more your business stresses safe cyber habits, the more aware your employees will be.
Policies and procedures are very important; but they are not enough. As cyber attacks have become more sophisticated and deceptive, it’s critical that you equip your team with basic security knowledge of what the threats are and how to identify the warning signs that might indicate a cybersecurity risk. If they don’t know what to look for, it’s hard to protect them… and your business.
Employee security training can take many forms. However, it should be an ongoing process. We provide clients with a dedicated online platform to educate employees on common cyber threats and ways to identify a malicious email or compromised website. In addition to video training, online quizzes and follow-up articles help increase awareness.
Is my security awareness training against phishing and other cyberattacks working?
The only way to know whether security awareness training and your mandated security solutions are working or not is through testing. This can be as simple as an employee security survey administered by your IT or HR team or random desk checks to verify adherence to physical access and password policies.
Even better, ongoing testing can identify areas where more training is needed and provide more customized education. For example, our security training provides an online platform by which you can track individual employee training progress. This is used in conjunction with simulated phishing attacks where your employees are sent fake phishing email messages. If a person falls for the phishing test, they are automatically redirected to additional security training.
Testing and enforcement does not have to be negative or derogatory. Focus on the intent of protecting both the business and the individual. Without actual application of the policies, even employees with the best of intentions may quickly let their guards down and become victims of a cyberattack. A training program or education platform is only effective if it is enforced.
As a business owner, your employees are one of your greatest assets and, simultaneously, your biggest IT security risk. The good news is that it doesn’t have to stay that way. Provide them with knowledge and equip them with the tools they need to protect themselves and your business's sensitive information.
Want your employees to be data security assets, not threats?
We work with clients to design security training and policies to equip your team with what they need to be savvy cyber users who can protect themselves and your business against cyber criminals and all cybersecurity threats.